May 19, 2025
Data-Broke: U.S. Tech Firms’ Counterintelligence Dilemma
By Gavin Wilde
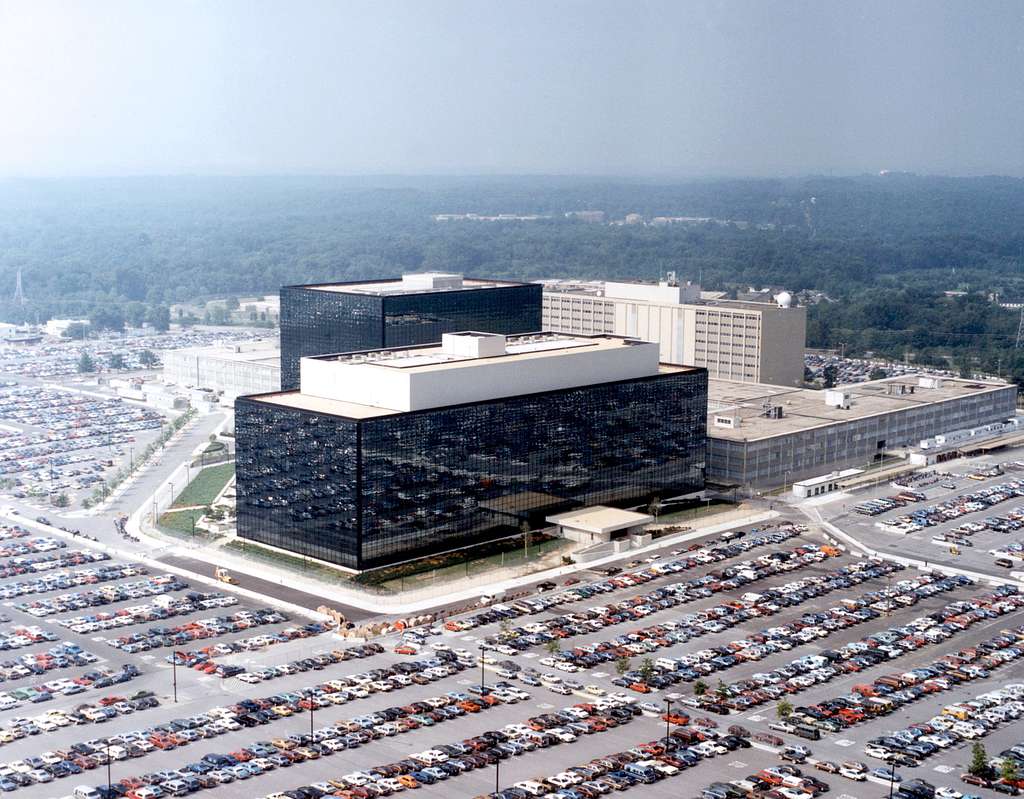
Nearly a decade has passed since the breach of the U.S. Office of Personnel Management (OPM) by Chinese state-backed hackers in the spring of 2015. That the operation netted Beijing the detailed backgrounds and personal data of over twenty million federal employees, clearance-holders, and applicants, as well as that of their co-habitants and spouses, constituted one of the most damaging counterintelligence breaches in U.S. history. Assessing the loss, former Central Intelligence Agency (CIA) and National Security Agency (NSA) chief Michael Hayden offered a blunt, sobering take: “It remains a treasure trove of information that is available to the Chinese [Communist Party] until the people represented by that information age off. There’s no fixing it.” In his estimation, the impact of the breach would take a generation or more to fully subside, until the youngest members of the federal workforce at that time ultimately retired.
Over the following decade, it would become clear that such counterintelligence hazards would hardly subside at all for reasons that were not yet fully evident, but still perhaps predictable. The aggregation of personal and location data on American consumers, including military service members, intelligence officers, national security officials, and contractors, would become part and parcel of the data-driven advertising behemoth that underpins the modern digital economy. While the threat of sophisticated cyber breaches into sensitive datasets remains, another trend is both an addition and contributor to the hacking risk: there is little need to steal through cunning espionage what can be obtained through little cost or effort in a vast and open data marketplace.
The question is whether such a status quo can be sustained without causing irrevocable damage to the counterintelligence interests of the United States. Can consumer data be treated as a “strategic resource,” as the most recent National Counterintelligence Strategy asserts, from both the commercial and security perspectives simultaneously? Or will one necessarily come at the expense of the other? As the age of “Big Data” and advances in computing have birthed the Artificial Intelligence era, these questions require urgent attention from policymakers. In what follows, we argue that they have, indeed, at critical points come into underappreciated but serious tension.
The Latest

April 23, 2026

Featuring Rosemary Kelanic
April 23, 2026

Featuring Rosemary Kelanic
April 23, 2026

Featuring Jennifer Kavanagh
April 23, 2026
Events on Grand strategy





